I was working on an AWS EC2 server today. My project was to build a shared hosting servers for a client. They are a shared hosting provider and I was assigned to build their infrastructure on AWS. They opted to use Virtualmin as their server panel and I configured their servers with Virtualmin and LEMP.
I usually use port 22 (sftp) for transfering files. But it wasn't an option in this case. Although I could still transfer files using sftp, client must give ftp access to their customers. FTP access is not a problem with Virtualmin since it automatically configures ProFTPD server. So I tested the FTP connection and this was the result I got.
Status: Connecting to xx.xx.xx.xx:21...
Status: Connection established, waiting for welcome message...
Status: Initializing TLS...
Status: Verifying certificate...
Status: TLS connection established.
Status: Logged in
Status: Retrieving directory listing...
Status: Server sent passive reply with unroutable address. Using server address instead.
Command: MLSD
Error: Directory listing aborted by user
Status: Disconnected from server
As you can see, the connection was failing. This is due to Firewall blocking connections. As it turns out, FTP in Passive Mode requires more ports to be opened to bypass NAT firewall limitations. So let's fix Server sent passive reply with unroutable address. Using server address instead error and get FTP working on EC2 instance.
Step #1: Specify Passive Port Range in ProFTPD configuration
The file you need to edit is
/etc/proftpd/proftpd.conf
You can either use nano text editor over SSH or go to Webmin > Servers > ProFTPD Server > Edit Config Files to edit this file.
Now look for following line and uncomment it (Delete the #)
# PassivePorts 49152 65534
You can change the port rage as you wish and narrow the range as you wish. I'm sticking to default range for this tutorial.
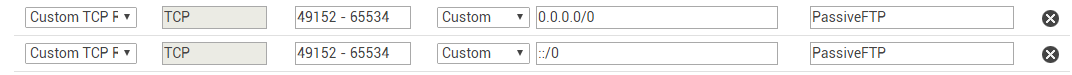
Step #2: Allow ProFTPD passive port range in EC2 security group
Now go to your EC2 security group and edit inbound rules to enable 49152 - 65534 port range. This is not necessary if you're not using EC2 security group to block connections.
For those who use EC2 security group, here's how it looks,
Step #3: Allow ProFTPD passive port range in UFW
Third and last step is to allow 49152 - 65534 port range in UFW. This is not necessary if you're not using UFW.
For those who use UFW, following command will do the trick.
ufw allow 49152:65534/tcp
This will fix the connection error. Although you'll still see the message Server sent passive reply with unroutable address. Using server address instead, FTP should work as normal.
